Introduction
Ledger wallets are among the most trusted hardware wallets in the world, designed to protect your cryptocurrency with industry-leading security standards. The Ledger Login process ensures that only you can access and manage your assets, with your private keys securely stored offline. This guide will walk you through everything you need to know about Ledger Login, including setup, security practices, features, and troubleshooting.
Why Secure Login Matters
Unlike traditional accounts, cryptocurrency wallets cannot be reset with a simple “forgot password” option. Once your private keys are lost or compromised, your funds could be irretrievable. Ledger Login is designed to prevent unauthorized access by requiring both the hardware device and your PIN, making it nearly impossible for hackers to access your assets remotely.
Steps to Login to Your Ledger Wallet
To access your Ledger wallet securely, follow these steps:
- Connect Your Device: Plug in your Ledger Nano S Plus or Ledger Nano X via USB or Bluetooth.
- Enter Your PIN: Use the physical buttons on the device to input your unique PIN code.
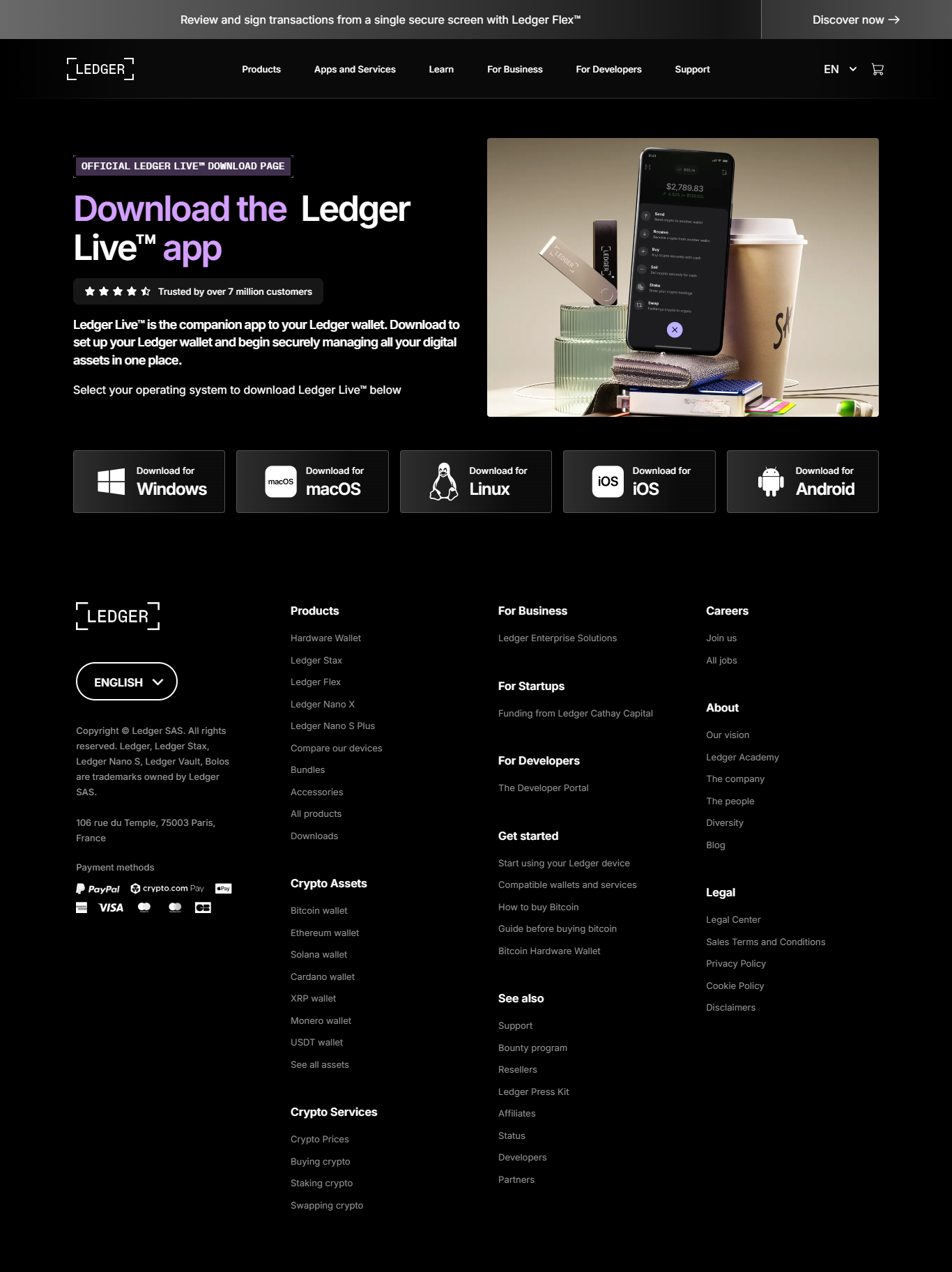
- Open Ledger Live: Download and launch the Ledger Live application on your computer or mobile device.
- Authenticate: The device will confirm all transactions before approval.
- Access Your Accounts: Once verified, you can view balances, send/receive crypto, stake tokens, or explore DeFi apps.
Ledger Live & Login Integration
Ledger Live acts as the bridge between you and your Ledger hardware wallet. While Ledger Live provides a user interface for transactions and portfolio tracking, the actual security lies in the Ledger device. Any attempt to move funds must be confirmed directly on the device, protecting you from phishing and malware-based attacks.
Security Features of Ledger Login
- ✅ PIN Protection: Prevents unauthorized access even if the device is stolen.
- ✅ Recovery Phrase: A 24-word seed phrase that allows you to restore your wallet on a new device.
- ✅ Offline Storage: Private keys never leave the Ledger device.
- ✅ Device Verification: Every action requires physical confirmation on your Ledger.
- ✅ Firmware Updates: Regular security updates from Ledger protect against new threats.
Best Practices for Secure Login
To maximize the security of your Ledger login, follow these best practices:
- 💡 Never share your 24-word recovery phrase with anyone.
- 💡 Always confirm URLs when accessing Ledger Live.
- 💡 Use strong PINs and avoid simple combinations.
- 💡 Keep your device firmware updated to the latest version.
- 💡 Store your recovery phrase offline in a fireproof and waterproof safe.
Troubleshooting Ledger Login Issues
Sometimes users may encounter issues when logging into their Ledger wallet. Here are common problems and solutions:
- Forgotten PIN: Reset your device and restore using your recovery phrase.
- Device Not Recognized: Ensure drivers are updated and use an original USB cable.
- Ledger Live Connection Errors: Update to the latest version of Ledger Live.
- Phishing Warnings: Only trust Ledger’s official channels and never input your recovery phrase online.
Conclusion
The Ledger Login process is designed to offer maximum security while remaining user-friendly. By combining hardware authentication with PIN verification and Ledger Live, users can confidently manage their cryptocurrency without fear of remote attacks. Always stay vigilant, keep your recovery phrase safe, and follow best practices to ensure your crypto remains protected.
With Ledger, your assets are yours—secured by state-of-the-art technology and protected by your vigilance. Ledger Login is more than just a password entry—it is the gateway to safe and secure cryptocurrency management.